A cybersecurity framework is a structured set of guidelines that helps your business manage security risks. Instead of guessing at what to protect and how, a framework gives you a prioritized checklist. For small and mid-sized businesses, especially law firms, accounting firms, and other professional services, the right framework can mean the difference between being protected and being exposed.
The problem is that most cybersecurity framework guides are written for enterprise IT teams with dedicated security departments. This one isn't. We'll break down the three frameworks that actually matter for small businesses (NIST, CIS Controls, and ISO 27001) and tell you which one to start with.
The Three Frameworks That Matter
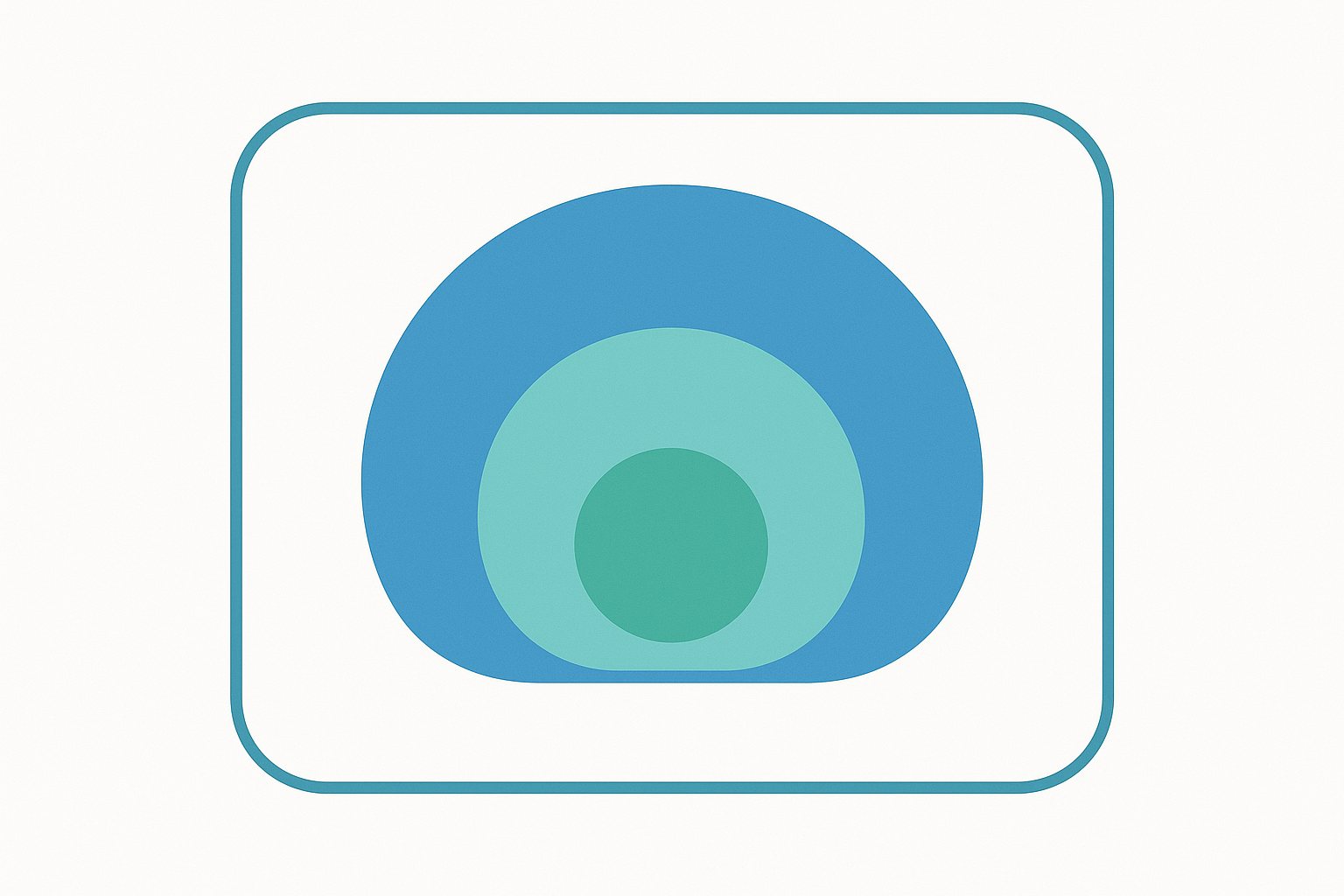
There are dozens of cybersecurity frameworks out there, but for small and mid-sized businesses, three are worth understanding. Each serves a different purpose.
NIST Cybersecurity Framework (CSF)
The NIST Cybersecurity Framework was developed by the National Institute of Standards and Technology and is the most widely referenced cybersecurity framework in the United States. It's voluntary, flexible, and designed to work for organizations of any size.
NIST CSF 2.0 organizes cybersecurity into six core functions:
- Govern: Establish your cybersecurity strategy, risk tolerance, and policies. This function was added in CSF 2.0 to emphasize that security starts with leadership and organizational commitment.
- Identify: Know what you have. Map your devices, data, software, and the risks they face.
- Protect: Put safeguards in place. Access controls, encryption, training, and secure configurations.
- Detect: Monitor for threats. Logging, alerting, and anomaly detection so you know when something is wrong.
- Respond: Have a plan for when something goes wrong. Incident response procedures, communication plans, and containment strategies.
- Recover: Get back to normal. Backup restoration, lessons learned, and improvements to prevent it from happening again.
Who it's for: Any business that wants a broad, strategic view of their cybersecurity posture. NIST is particularly useful if you need to communicate your security approach to clients, partners, or regulators. Law firms answering ABA compliance questions and accounting firms meeting FTC Safeguards Rule requirements often use NIST as their reference framework.
Practical takeaway: NIST tells you what to think about, but not exactly how to do it. It's the strategy layer. Most small businesses need to pair it with something more tactical.